Israel’s AI Revolution — Part 4
NSO’s Reinvention
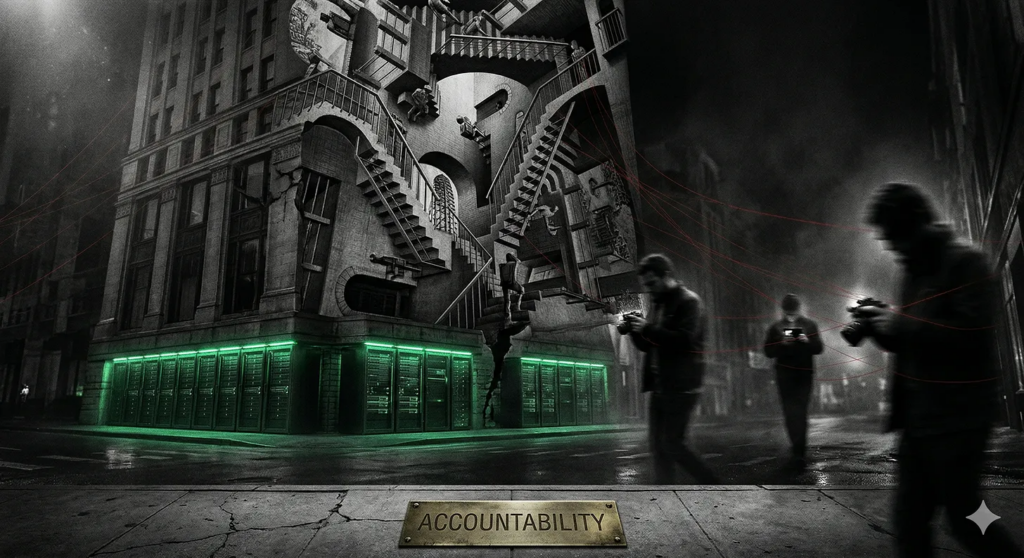
In January 2026, NSO Group released a new transparency report. The company said it was entering “a new phase of accountability.” The document gave away almost nothing: fewer disclosures than in prior years, no customer numbers, no country names, no meaningful account of investigations into misuse. It read less like transparency than reputation management. And that may be the point.
The real story is not the report itself. It is the structure beneath it. In late 2025, a U.S.-led investor group headed by Hollywood producer Robert Simonds acquired NSO Group — the Israeli spyware company that Washington blacklisted in 2021 for enabling the surveillance of journalists, activists, and government officials worldwide. Former Trump ambassador to Israel David Friedman was installed as executive chairman. The founding CEO stepped down. The last remaining co-founder left. And the logic of the restructuring became clear: the U.S. Entity List targets foreign companies. If NSO is now American-owned and American-led, the restriction that was supposed to contain it may no longer apply.
The most notorious cyberweapon in the world is not disappearing. It is changing its address.
* * *
Born from the Unit
NSO Group was founded in 2010 by Niv Karmi, Omri Lavie, and Shalev Hulio. Lavie and Hulio were Israeli tech entrepreneurs with ties to Unit 8200, the elite signals intelligence division of the Israeli military. Karmi handled the technical side and reportedly had his own intelligence and security background. The company’s most valuable engineers are graduates of the military’s advanced cyber weapons training programs, and almost all of its research staff came from military intelligence. By the time NSO attracted international attention, it employed over 700 people globally. This was never a software company that drifted into defense work. It was a military capability structured as a private company from the start.
That distinction matters. In Israel, Pegasus is classified as a weapon and treated as controlled military technology, not an ordinary commercial product. Every export requires approval from the Defense Ministry. The state does not merely regulate NSO. It enables it, supervises it, and, when useful, deploys it as a diplomatic instrument — Pegasus reportedly played a role in building Arab support for the Abraham Accords in 2020. The company exists at the intersection of Israeli state power and private enterprise, and that intersection is not incidental. It is the design.
That is why NSO sits in such a morally and politically ambiguous place. It is private enough to export blame, but state-connected enough to serve strategic interests. The result is a system built for plausible deniability.
* * *
What Pegasus Is
Pegasus is not a surveillance tool in the old sense. It is a full-device compromise system. It can enter a phone without a click, evade ordinary defenses, and turn a target’s device into a live feed: messages, photos, contacts, microphone, camera, location, all potentially exposed. It does not merely intercept communications. It jumps over encryption entirely by attacking the device itself.
And it does not stand still. During the WhatsApp trial, NSO was forced to acknowledge that the company spends tens of millions of dollars annually developing new methods of installation — through instant messaging platforms, browsers, and operating systems — and that Pegasus remains capable of compromising any iOS or Android device to this day. This is not a product someone buys. It is an offensive capability someone subscribes to.
NSO has long argued that its tools are intended for legitimate law enforcement and counterterrorism. The public record tells a different story. Pegasus was used to monitor the inner circle of journalist Jamal Khashoggi before his murder in the Saudi consulate in Istanbul in 2018. It has been linked to the surveillance of heads of state, including Emmanuel Macron and Cyril Ramaphosa, and to targeting campaigns against human rights defenders, lawyers, political dissidents, and activists across dozens of countries. The 2019 WhatsApp campaign alone compromised roughly 1,400 users in 51 countries. By now, Pegasus is not just a spyware product. It is a symbol of what happens when state power, private capital, and digital intrusion converge.
* * *
Gaza as Testbed
While Pegasus has been deployed against heads of state and activists globally, its most intensive application remains closest to home. After October 7, Israeli agencies reportedly used advanced surveillance capabilities to track kidnapped and missing Israelis and to monitor suspected Hamas operatives. NSO established what was described as a “war room” alongside former employees and similar companies to assist in the effort. On the surface, that is a politically powerful use case: few people will object to finding hostages or stopping attacks. But wartime necessity has a way of widening the boundaries of what becomes normal.
That is where the deeper concern begins. The pattern predates the war. In 2021, researchers found Pegasus infections on phones belonging to staff at six Palestinian civil society organizations, including Al-Haq and Defense for Children International–Palestine. Within months, the Israeli government designated all six as terrorist organizations — a move condemned by human rights groups and rejected by European governments as politically motivated. No evidence supporting the designations was made public. The sequence is difficult to read as coincidence: surveillance, then criminalization.
NSO-linked sources acknowledged after October 7 that they did not know whether safeguards existed to prevent broader surveillance of the Palestinian population. That is not an accusation. It is an absence — and in the context of a company whose product has already been used against the people it is now deployed among, the absence is the point.
What gets field-tested in Gaza does not stay in Gaza. It becomes part of the exportable mythology of the product.
* * *
The Cloud Layer
If Pegasus is the weapon, then the cloud is the substrate. The Nimbus contract — the $1.2 billion deal involving Google and Amazon — is not a separate story. It is the infrastructure that helps keep the larger system alive.
The important point is not that the cloud fires the spyware. It is that cloud systems store, process, and analyze the data that surveillance and intelligence operations produce. That makes the hyperscalers part of the same architecture, even if they prefer to describe themselves as neutral service providers. Google and Amazon have maintained that Nimbus involves no weapons development. The contract’s actual terms tell a different story.
According to a joint investigation by the Guardian, +972 Magazine, and Local Call, based on leaked documents, Google and Amazon agreed to a coded reporting system — referred to as the “winking mechanism” — to notify Israel when they are compelled to hand data to a foreign government. The system works through payments keyed to international telephone codes: NIS 1,000 for a U.S. request, NIS 3,900 for Italy, and a flat NIS 100,000 if the companies are legally barred from identifying the requesting country at all. Legal analysis presented in the investigation described this as a circumvention of U.S. and European laws prohibiting such disclosures. The companies also agreed that they cannot suspend or revoke Israel’s access to their services, even if Israel violates their standard terms of use — a provision with no known equivalent in any other sovereign cloud deal.
That contractual structure explains why Microsoft was the one to blink — and why its action, far from challenging the system, only confirmed how well the system works. In September 2025, Microsoft partially suspended Azure cloud and AI services to Israel’s Unit 8200 — the same signals intelligence unit from which NSO draws most of its workforce — after an internal review found that millions of intercepted Palestinian civilian phone calls were being stored and analyzed on its systems. Microsoft could act only because its contract with the Defense Ministry was a standard commercial agreement, not part of Nimbus. It was the exception, and its limits proved the rule: the data reportedly migrated to AWS — which, under Nimbus, could not have taken the same step.
The weapon does not function in a vacuum. It functions inside an American-built stack.
* * *
The Reckoning That Wasn’t
The WhatsApp lawsuit was supposed to be the moment the legal system caught up. In some ways it did — further than anyone expected. In December 2024, a federal judge found NSO Group liable for hacking WhatsApp users and breaching federal and state computer fraud laws. In May 2025, a jury ordered NSO to pay approximately $167 million in punitive damages — the first verdict against a commercial spyware company in U.S. history. WhatsApp called it “a critical deterrent to this malicious industry.”
Then the architecture reasserted itself. In October 2025, the same judge issued a permanent injunction barring NSO from targeting WhatsApp — but reduced the damages from $167 million to roughly $4 million. The reasoning: there have not been enough cases involving unlawful electronic surveillance in the smartphone era for the court to conclude that NSO’s conduct was “particularly egregious.” A company linked to the surveillance of journalists, heads of state, and civilian populations across 51 countries had its penalty cut by more than ninety-seven percent — not because the court doubted the wrongdoing, but because the legal system had no precedent for measuring it.
The injunction itself was narrow. It covered WhatsApp. It did not extend to Facebook, Instagram, Threads, or any other Meta platform. NSO was ordered to stop reverse-engineering WhatsApp and to delete its source code. It was not ordered to stop selling Pegasus.
Meanwhile, other fronts collapsed. Apple dropped its own lawsuit against NSO in 2024, citing concerns that continuing it would expose sensitive details of its security methods. No major cloud provider has faced any legal consequence for its role in the broader infrastructure. Google and Amazon employees who protested Nimbus were fired. Microsoft partially suspended services and the data moved elsewhere. Worker dissent has been visible. Legal accountability has not.
The reckoning arrived, but only in fragments — and the fragments were small enough for NSO to step over.
* * *
The Reinvention
By early 2026, the reinvention was well underway. The American investor group led by Robert Simonds had taken control. David Friedman, former U.S. ambassador to Israel under Trump, was installed as executive chairman. CEO Yaron Shohat stepped down. Omri Lavie, the last remaining co-founder still involved with the company, departed. Meanwhile, Shalev Hulio — the other co-founder, the man who once introduced himself at an investors’ dinner by saying “I’m the founder of NSO” to nervous laughter — had already moved on to a new billion-dollar cybersecurity startup called Dream Security. The old leadership was gone. The new leadership was American, politically connected, and pointed at Washington.
The lobbying apparatus matched the ambition. Since 2018, NSO has hired more than fifteen lobbying, law, and public relations firms in the United States, spending at least $7.6 million between 2020 and 2024 alone. The company poured over $1.8 million into Republican political campaigns during the 2024 election cycle. Earlier lobbyists registered under the Foreign Agents Registration Act, which requires disclosure of specific meetings. The newer ones registered under the Lobbying Disclosure Act, which does not. The campaign was not only growing. It was becoming harder to see.
The strategy has a clear structural logic. The Entity List targets foreign companies. If NSO’s ownership, leadership, and corporate structure are American, the designation may become functionally irrelevant — not overturned, just outgrown. No one needs to win the argument in Washington if the legal category no longer fits.
The question is no longer whether NSO can survive. It is whether a cyberweapon linked to the surveillance of journalists, dissidents, heads of state, and civilian populations can be made respectable by changing its country of incorporation.
* * *
Parts 1 through 3 of this series traced the military AI ecosystem, the rules of war in the age of algorithms, and the regulatory landscape around autonomous weapons. This piece has shown what holds all of it together: not just technology, not just policy failure, but an integrated system in which state power, private enterprise, cloud infrastructure, and legal maneuvering fit together with an elegance that ought to disturb us.
NSO was blacklisted, sued, sanctioned, investigated, and found liable in a landmark verdict. It survived all of it. Not by winning the arguments, but by making them irrelevant — restructuring around the restrictions the way water moves around a stone. The Entity List still exists. The injunction still stands. The company is fine.
That is what impunity looks like when it is well-built. Not the absence of accountability, but a system so structurally adaptable that accountability becomes decorative. The verdict hangs on the wall. The weapon ships on schedule.
Sources
Amnesty International. “Ruling against NSO Group in WhatsApp Case a ‘Momentous Win in Fight against Spyware Abuse.’” May 9, 2025. https://www.amnesty.org/en/latest/news/2025/05/ruling-against-nso-group-in-whatsapp-case-a-momentous-win/.
Avraham, Yuval, et al. “Amazon, Google Agreed to Inform Israel on Data Handed to Foreign Governments.” Joint investigation by the Guardian, +972 Magazine, and Local Call, reported via Jerusalem Post, October 30, 2025. https://www.jpost.com/israel-news/article-872152.
Chin-Rothmann, Caitlin. “Cyber Mercenaries: Limiting Government Use of Commercial Spyware.” Georgetown Journal of International Affairs, September 4, 2024. https://gjia.georgetown.edu/2024/09/04/cyber-mercenaries-limiting-government-use-of-commercial-spyware/.
Franceschi-Bicchierai, Lorenzo. “Critics Pan Spyware Maker NSO’s Transparency Claims amid Its Push to Enter US Market.” TechCrunch, January 8, 2026. https://techcrunch.com/2026/01/08/critics-pan-spyware-maker-nsos-transparency-claims-amid-its-push-to-enter-us-market/.
Franceschi-Bicchierai, Lorenzo. “NSO Group Must Pay More Than $167 Million in Damages to WhatsApp for Spyware Campaign.” TechCrunch, May 6, 2025. https://techcrunch.com/2025/05/06/nso-group-must-pay-more-than-167-million-in-damages-to-whatsapp-for-spyware-campaign/.
Franceschi-Bicchierai, Lorenzo. “Spyware Maker NSO Group Confirms Acquisition by US Investors.” TechCrunch, October 10, 2025. https://techcrunch.com/2025/10/10/spyware-maker-nso-group-confirms-acquisition-by-us-investors/.
Hatami, David M. “Washington’s Pegasus Spyware Problem.” TechPolicy.Press, December 17, 2025. https://www.techpolicy.press/washingtons-pegasus-spyware-problem/.
Kovacs, Eduard. “NSO Ordered to Stop Hacking WhatsApp, but Damages Cut to $4 Million.” SecurityWeek, October 20, 2025. https://www.securityweek.com/nso-ordered-to-stop-hacking-whatsapp-but-damages-cut-to-4-million/.
Lyngaas, Sean. “NSO Group Owes $168M in Damages to WhatsApp over Spyware Infections, Jury Says.” CyberScoop, May 7, 2025. https://cyberscoop.com/nso-group-owes-whatsapp-over-spyware-infections-jury/.
Meta. “Winning the Fight against Spyware Merchant NSO.” About Meta (blog), May 6, 2025. https://about.fb.com/news/2025/05/winning-the-fight-against-spyware-merchant-nso/.
NSO Group. “2025 Transparency and Responsibility Report.” January 8, 2026. https://www.nsogroup.com/wp-content/uploads/2026/01/2025-Transparency-and-Responsibility-Report.pdf.
Panagiotopoulos, Vas. “Will NSO’s US Lobbying Pay Off under Trump?” TechPolicy.Press, March 2026. https://www.techpolicy.press/will-nsos-us-lobbying-pay-off-under-trump/.
Reuters. “Israel Picks Amazon’s AWS, Google for Flagship Cloud Project.” April 21, 2021. https://www.reuters.com/world/middle-east/israel-picks-amazons-aws-google-flagship-cloud-project-2021-04-21/.
Reuters. “US Judge Finds Israel’s NSO Group Liable for Hacking in WhatsApp Lawsuit.” December 23, 2024. https://www.reuters.com/technology/cybersecurity/us-judge-finds-israels-nso-group-liable-hacking-whatsapp-lawsuit-2024-12-23/.
Schectman, Joel, and Christopher Bing. “Pegasus Spyware Maker NSO Is Conducting a Lobbying Campaign to Get Off U.S. Blacklist.” ProPublica, July 12, 2022. https://www.propublica.org/article/pegasus-spyware-nso-israel-blacklist-lobbying.
Simons, Matt. “Meta Wins $168 Million in Damages from Israeli Cyberintel Firm in WhatsApp Spyware Scandal.” Courthouse News Service, May 6, 2025. https://www.courthousenews.com/meta-wins-168-million-in-damages-from-israeli-cyberintel-firm-in-whatsapp-spyware-scandal/.
Srivastava, Mehul. “NSO Group’s Founder Returns with $1 Billion Startup Dream Security.” Bloomberg, December 25, 2025. https://www.bloomberg.com/news/articles/2025-12-22/nso-group-s-founder-returns-with-1-billion-startup-dream-security.
“Spyware Firm NSO’s Chief Steps Down as U.S. Lifts Sanctions on Intellexa Executives.” Haaretz, January 1, 2026. https://www.haaretz.com/israel-news/security-aviation/2026-01-01/ty-article/.premium/spyware-firm-nsos-chief-steps-down-as-u-s-lifts-sanctions-on-intellexa-executives/.
Swan, Jonathan, and Barak Ravid. “Israel’s NSO Unleashes Controversial Pegasus Spyware in Gaza Conflict.” Axios, November 14, 2023. https://www.axios.com/2023/11/14/pegasus-nso-hamas-israel-spyware.
Torbati, Yeganeh, Sam Biddle, and Josh Harkinson. “A Notorious Israeli Spyware Firm Wants to Use the Gaza War to Make a Comeback.” The Hill, January 27, 2024. https://thehill.com/opinion/cybersecurity/4433419-a-notorious-israeli-spyware-firm-wants-to-use-the-gaza-war-to-make-a-comeback/.
U.S. Commerce Department. “Commerce Adds NSO Group and Other Foreign Companies to Entity List.” Press release, November 3, 2021.
“US Court Bars Israeli Spyware Firm from Targeting WhatsApp Users.” Al Jazeera, October 18, 2025. https://www.aljazeera.com/news/2025/10/18/us-court-bars-israeli-spyware-firm-from-targeting-whatsapp-users.
